Docker For Mac Docker Daemon Json Config
Click on the Docker icon from the menu bar and then Preferences. Click Reset to reset to factory defaults, restart the Docker daemon, reset Kubernetes cluster, or to reset the disk image. The Diagnose and Feedback option allows you troubleshoot any issues you may be experiencing with Docker Desktop Enterprise. Jump to Gatherering Docker daemon metrics on MacOS - If you're a Docker-for-mac user, then there's a little difference. First, you'll not have the /etc/docker/daemon.json file. From tweaking the daemon configurations though.
Estimated reading time: 4 minutesWhile it’s highly recommended to secure your registry using a TLS certificateissued by a known CA, you can choose to use self-signed certificates, or useyour registry over an unencrypted HTTP connection. Either of these choicesinvolves security trade-offs and additional configuration steps.
Deploy a plain HTTP registry
Warning:It’s not possible to use an insecure registry with basic authentication.
This procedure configures Docker to entirely disregard security for yourregistry. This is very insecure and is not recommended. It exposes yourregistry to trivial man-in-the-middle (MITM) attacks. Only use this solution forisolated testing or in a tightly controlled, air-gapped environment.
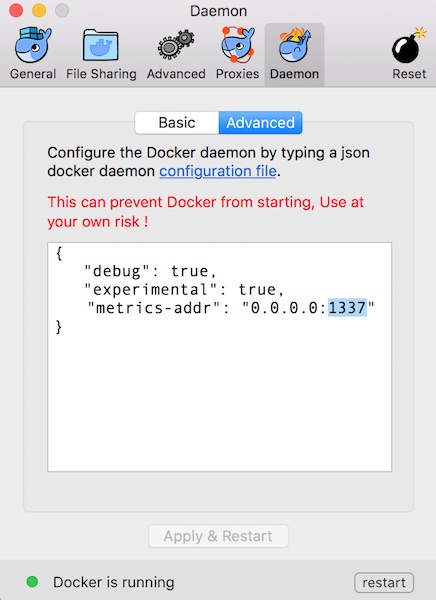
Edit the
daemon.jsonfile, whose default location is/etc/docker/daemon.jsonon Linux orC:ProgramDatadockerconfigdaemon.jsonon Windows Server. If you useDocker Desktop for Mac or Docker Desktop for Windows, click the Docker icon, choosePreferences, and choose +Daemon.If the
daemon.jsonfile does not exist, create it. Assuming there are noother settings in the file, it should have the following contents:Substitute the address of your insecure registry for the one in the example.
With insecure registries enabled, Docker goes through the following steps:
- First, try using HTTPS.
- If HTTPS is available but the certificate is invalid, ignore the errorabout the certificate.
- If HTTPS is not available, fall back to HTTP.
- First, try using HTTPS.
Restart Docker for the changes to take effect.
Repeat these steps on every Engine host that wants to access your registry.
Use self-signed certificates
Warning:Using this along with basic authentication requires to also trust the certificate into the OS cert store for some versions of docker (see below)
This is more secure than the insecure registry solution.
To do so, choose View menu Use Large Fonts. After changing to large fonts, there are a few ways you can.If you have difficulty using a computer mouse, you can:. Increase the font size used for the majority of text in Quicken. If you have a visual impairment, you can:. Quicken mac shortcuts. Note that the minimum recommended display resolution for large fonts is 1280x1024 for Quicken Home & Business and Quicken Rental Property Manager, or 1280x800 for all other versions of Quicken.
Generate your own certificate:
Be sure to use the name
myregistrydomain.comas a CN.Use the result to start your registry with TLS enabled.
Instruct every Docker daemon to trust that certificate. The way to do thisdepends on your OS.
Linux: Copy the
domain.crtfile to/etc/docker/certs.d/myregistrydomain.com:5000/ca.crton every Dockerhost. You do not need to restart Docker.Windows Server:
Open Windows Explorer, right-click the
domain.crtfile, and choose Install certificate. When prompted, select the followingoptions:Store location local machine Place all certificates in the following store selected Click Browser and select Trusted Root Certificate Authorities.
Click Finish. Restart Docker.
Docker Desktop for Mac: Follow the instructions onAdding custom CA certificates.Restart Docker.
Docker Desktop for Windows: Follow the instructions onAdding custom CA certificates.Restart Docker.
Troubleshoot insecure registry
This section lists some common failures and how to recover from them.
Failing..
Failing to configure the Engine daemon and trying to pull from a registry that is not usingTLS results in the following message:
Docker still complains about the certificate when using authentication?
When using authentication, some versions of Docker also require you to trust thecertificate at the OS level.
Ubuntu
Red Hat Enterprise Linux
Oracle Linux
Restart Docker for the changes to take effect.
Windows
Open Windows Explorer, right-click the certificate, and chooseInstall certificate.
Then, select the following options:
- Store location: local machine
- Check place all certificates in the following store
- Click Browser, and select Trusted Root Certificate Authorities
- Click Finish
Learn more about managing TLS certificates.
After adding the CA certificate to Windows, restart Docker Desktop for Windows.
registry, on-prem, images, tags, repository, distribution, insecure